A security breach can shut down operations and leave a trail of collateral damage in its wake. While worldwide awareness of cyber attacks and their effect on organizations of all sizes has increased significantly over the years, many organizations lack incident response and recovery plans.
Business leaders should use cyber threat intelligence and security validation processes to test all aspects of their security strategy to know where they stand and how to protect against future attacks. Each phase within the attack lifecycle must be addressed to improve breach resilience and mitigate impacts to business continuity.
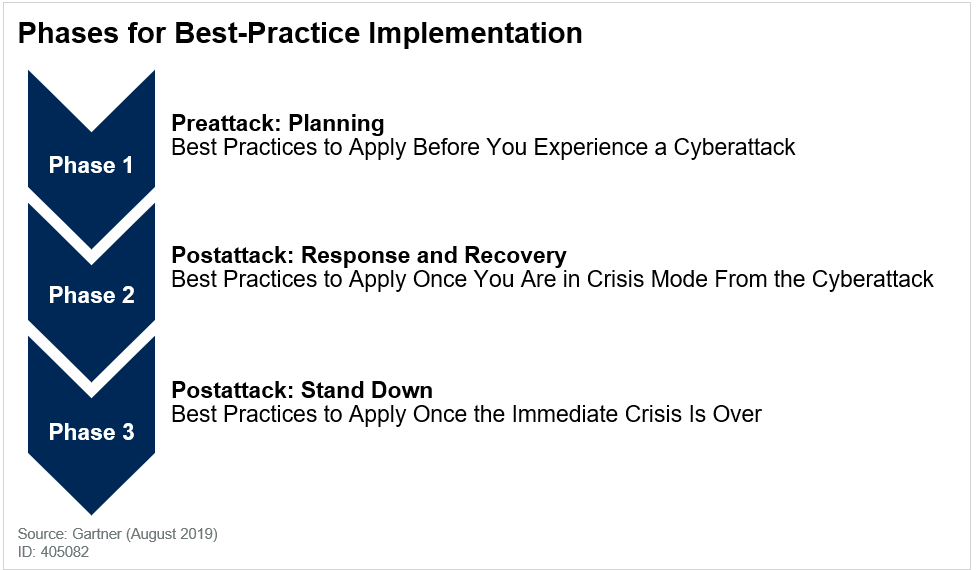
FireEye experts have derived several recommendations on cyber attack preparedness and response from Gartner’s recent cyber security report. Download your complimentary copy to learn about:
- Characteristics of a cyber attack
- Forming holistic cyber attack response teams
- Crisis management and communications planning
- Damage assessment following a breach
- Stand-down process

